|
Getting your Trinity Audio player ready...
|
Contents
- What Is IT Security?
- What is Application Security?
- Web, Cloud & Mobile Application Security
- Application Security Best Practices
What Is IT Security?
Increased security concerns are one of the top drivers (59%) of IT budget increases in 2019, according to the Spiceworks State of IT 2019 report. It’s no surprise with hackers becoming ever more sophisticated and large security breaches affecting businesses of all sizes.
IT security is the practice of protecting your sensitive digital information from cyber threats like malware (malicious software) including viruses, spyware and ransomware. It encompasses the securing of your business hardware, software, networks and data all of which present unique vulnerabilities. IT security can be costly, but it’s an investment worth making to prevent breaches that can have a devastating impact on your business.
While each business will have different IT security needs, there are a few common types to consider.
-
Network Security: Protecting all elements of your network, including hardware and software, from hackers gaining access. Engineering your networks with security in mind involves some pro-active measures like vulnerability assessments and penetration testing.
- Internet Security: A broad term also known as cyber security, used to describe the measures by which internet user access and internet data flow is secured to prevent data sharing. Encryption and security software are just a couple of tools you can explore.
- Endpoint Security: This refers to protecting the devices your employees are using, such as desktops, laptops, tablets or mobile phones. Only authorized devices should be accessing your network and users should be educated on security best-practices.
- Cloud Security: If your business data and applications reside in a public cloud like Microsoft Azure, you need to deploy a different set of security measures than for on premises hosting.
- Application Security: Security measures are coded directly into the application software. Let’s explore this one in more detail.
What Is Application Security?
There are different levels of software security that need to be addressed, but application security means developing features that will help protect the software that houses your business-critical data from external threats. This can include built-in security features such as authentication, authorization, encryption.
Almost any application can be vulnerable to exploitation regardless if it’s custom software, off-the-shelf, hosted on premises or in the cloud. But with the proper security measures in place, you can minimize the risk of cyber-attacks on your business applications and your data being stolen, modified or deleted.
Web, Mobile & Cloud Application Security
The type of security measures you implement largely depends on the location of your applications, their function and the type of data they contain.
-
Web Applications
Web-based applications are often customer-facing and may store sensitive customer data like personal or financial information. Incidentally, web applications tend to be the most vulnerable because they’re public, so you need to have the highest security measures in place. Firewalls are a virtual barrier between your web application and those trying to access it without authorized access. You can put your application to the test with penetration testing which involves trying to find and fix bugs in your own software before a hacker does. Some large organizations pay white hat hackers hundreds of thousands of dollars to find bugs in their software (if you’re curious about it, Google “bug bounty programs”). Data encryption and multi-factor authentication will also help keep your web application more secure.
-
Mobile Applications
Mobile applications carry a unique set of security requirements because they exist on various phone and tablet devices with different operating systems—each operating system comes with its own set of vulnerabilities. Plus, mobile devices can more easily be lost or stolen. In addition to making sure the application itself was written with security top-of-mind, you need to educate your users on device security. If the application is being used by your employees to access company data, make sure they’re setting up passwords, face or thumbprint ID, avoiding unsecured wireless networks and not clicking on suspicious links.
-
Cloud Applications
Hosting your applications on a cloud service like Microsoft Azure gives you access to their top-of-the-line security infrastructure. However, there’s still some configuration work and due diligence on your part. Review the exact security measures of the cloud provider to ensure they meet your business needs and fill in any gaps. For example, using HTTPS protocol and two-factor authentication to make sure the right people have access to the information they need to do their job, without opening your applications to everyone.
Application Security Best Practices
Your unique business requirements and the type of applications you’re using will dictate the security measures you’ll need to implement. Here are some best practices to consider.
- Use Firewalls: This is one of your first lines of defense against a cyber-attack. Implement external, internal network and VPN (virtual private network) firewalls.
- Use TLS (Transport Layer Security): Use HTTPS protocol to encrypt all communications between your browser and web servers receiving the information to prevent hackers from intercepting it.
- Keep Software Updated: Always have the latest version of any third-party software and work with your software development partner to keep any custom software secure and up to date.
- Plan for Mobile Security: If your employees are accessing applications via their mobile devices, have a mobile security policy in place complete with tips and regular security updates.
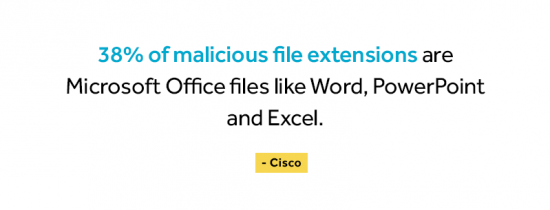
- Educate Employees: Document your security policies and regularly communicate them to your team. Educate employees on the importance of strong passwords, periodic password updates, how to spot suspicious links and downloads.
- Use Multifactor Authentication: Using a second form of authentication just adds an extra layer protection because it’s less likely that a hacker will have both sets of access points. Employee personal cell phone numbers are a common second authentication form.
- Regular Data Backup: Even if you take all the necessary precautions, you may still fall victim to a cyber-attack. Whether your data is stored in the cloud or on prem, back up critical information, like financial and customer data, in a separate location.
- Stay Informed: Be aware of the latest security threats. Learn more about which vulnerabilities to watch for in our post Why Application Security Is More Important Than Ever.
If you’re working with a company who is developing custom software or configuring applications such as Dynamics 365 or Office 365 for your business, be sure to ask them about their application security approach. Security should be top of mind throughout the development process—from the initial requirements gathering to design and post-deployment testing.
Conclusion
IT security concerns are without a doubt the biggest challenge and headache for most IT professionals. There are so many different touchpoints you need to secure—from network to endpoint devices—and so many ways to do it. Application security can be especially complicated if you’re managing multiple employee and customer facing web, mobile or cloud applications.
But with some planning and the right software development partner, you’ll be able to significantly minimize your security vulnerabilities.
Want to learn more about developing secure business applications? Let’s chat!